COMMERCIAL AND RESIDENTIAL SECURITY
Security You Can Trust
VinTech Systems is committed to protect your family, business, and investments.



Maintenance Services
Security systems run 24/7/365. It’s proven that the best way to extend the life of your security system is to perform regular maintenance. Furthermore, preventative services help optimize the performance of your system. This is especially important with outdoor equipment that is exposed to extreme weather.
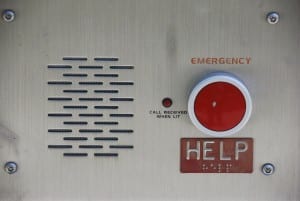
Emergency Call Boxes
How do you provide security to a parking lot or large isolated area? Installing Emergency Call Boxes offers direct connection to an operator or dispatcher in the event of an emergency.

Mobile Control
Do you ever forget to arm your alarm system or lower your thermostat? With remote access, you can control these devices with a simple click from your mobile app. Remote control right at your fingertips indeed!

Wireless Services
Do you feel safe in your neighborhood? Is your community secure? Wireless Surveillance Solutions are perfect for large areas, residential buildings, and commercial complexes. This cost-effective solution allows management to monitor multiple buildings at once. Additionally, wireless systems eliminate the hassle of wiring. This is the ideal solution to save you time and money.

Telephone Entry System
Can you imagine opening your front door right from your mobile phone? A Telephone Entry System enables you to give access without stepping out of your door.

Remote Technical Support
Having issues managing your security system? VinTech Security Systems offers unique remote services to provide immediate support, when you need it the most.
Case Study: Chinatown
Customized security for one of Chicago’s high-traffic neighborhoods.
The Chicago Chinatown neighborhood receives a large influx of people arriving by car and public transportation daily. While the neighborhood is considered relatively safe, community leaders had been discussing the ongoing security of their residents, businesses, and tourists.
In association with the Chicago Chinatown Chamber of commerce and CPD, VinTech systems was hired to determine key locations throughout the district to install 18 additional security cameras.


Who do we serve?
We work well with all sorts of businesses, including:
Choose VinTech Systems
Don’t settle for any company when it comes to safety and security. Choose our company that has a proven track record of success!

